WhatsApp zero-day bug: What you need to know

The internet is buzzing with warnings about the WhatsApp zero-day bug. These are two vulnerabilities silently fixed and reported by WhatsApp on 25th September 2022. The actual security advisory from WhatsApp can be found here. As pointed out by Paul Ducklin in the Naked Security Blog, it is not a "zero-day" vulnerability but rather a bug discovered by the developers themselves. Still, the consequences of a critical vulnerability, even in older versions of WhatsApp, can be far-reaching.
WhatsApp Affected Versions
1. CVE-2022-36934:
- Affected Vendors: WhatsApp
- Android prior to v2.22.16.12
- Business for Android prior to v2.22.16.12
- iOS prior to v2.22.16.12
- Business for iOS prior to v2.22.16.12
- CVE ID Advisory: CVE-2022-36934
- Disclosed by: Facebook Inc.
- CVSS Score: 9.8 CRITICAL
2. CVE-2022-27492
- Affected Vendors: WhatsApp
- Android prior to v2.22.16.2
- iOS prior to v2.22.15.9
- CVE ID Advisory: CVE-2022-27492
- Disclosed by: Facebook Inc.
- CVSS Score: 7.8 HIGH
Mitigate WhatsApp Zero Day
Keep your WhatsApp always updated! And as a general recommendation, do not install applications (APKs on Android) from unknown sources, such as those downloaded via the browser. Keep your application downloads limited to the official App stores on iOS and Android.
CVE-2022-36934 Integer Overflow Bug
From the security advisory,
1An integer overflow in WhatsApp for Android prior to v2.22.16.12, Business for Android prior to v2.22.16.12, iOS prior to v2.22.16.12, Business for iOS prior to v2.22.16.12 could result in remote code execution in an established video call.
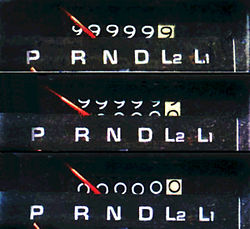
Consider the infamous odometer example for this case. The odometer resets when it hits 999999 --> 000000 instead of incrementing to 1000000.
What is an integer overflow exactly? A computer represents numbers (or integers) as binary (0s and 1s). Most computers today can handle numbers up to 64-bits. Because of the limit on number of bits present, an integer has a max limit (9,223,372,036,854,775,807). Depending on how the application is programmed, the application might try to go over the max limit. In that case, all kinds of undefined and weird behaviour can happen, which can be exploited by hackers.
In the WhatsApp case, according to GBHackers, the bug affects the Video Call Handler component of WhatsApp which allows an attacker to craft a specific payload to trigger a heap-based buffer overflow enabling them to take complete control of the application. A buffer overflow will enable hackers to rewrite the application memory, letting them overwrite existing data and execute their malicious code.
CVE-2022-27492 Integer Underflow Bug
From the security advisory,
1Integer underflow in WhatsApp for Android prior to v2.22.16.2 and WhatsApp for iOS v2.22.15.9 could have caused remote code execution when receiving a crafted video file.
What is an integer underflow exactly? Similar to the overflow, it turns out there is also a minimum limit of an integer (-9,223,372,036,854,775,808). Depending on how the application is programmed, the application might try to go below the minimum limit. In that case, all kinds of undefined and weird behaviour can happen, which can be exploited by hackers.
To learn more about Integers Overflows and Underflows, look at this blog.
In the WhatsApp case, according to GBHackers, the bug affects the Video File Handler component of WhatsApp which is manipulated to lead to a memory corruption vulnerability. As a result, the attackers can drop a crafted video file on the user's chat. Once the user interacts with the video, it will let the hackers take complete control of the victim's application.
History of WhatsApp Vulnerabilites
WhatsApp, which offers encrypted messaging by default to over 2 billion users worldwide, has always been a critical target for various attackers and hackers, bringing down one of the most dangerous exploits known to the Cybersecurity community.
- Even after launching end-to-end encryption in April 2016. As of September 2021, it is known that WhatsApp extensively uses outside contractors and artificial intelligence systems to examine user messages, images and videos; and turns them over to law enforcement metadata, including critical account and location information.
- In May 2019, a security vulnerability in WhatsApp was found and fixed that allowed a remote person to install spyware by making a call which did not need to be answered. In May 2019, WhatsApp was attacked by hackers who installed spyware on several victims' smartphones. The hack, allegedly developed by Israeli surveillance technology firm NSO Group, injected malware onto WhatsApp users' phones via a remote-exploit bug in the app's Voice over IP calling functions. A Wired report noted the attack was able to inject malware via calls to the targeted phone, even if the user did not answer the call.
- In December 2019, WhatsApp confirmed a security flaw allowing hackers to use a malicious GIF image file to access the recipient's data. The hack is triggered when the recipient opens the gallery within WhatsApp, even if not sending the malicious image, and the device and its contents become vulnerable. The flaw was patched, and users were encouraged to update WhatsApp.
- On December 17, 2019, WhatsApp fixed a security flaw that allowed cyber attackers to repeatedly crash the messaging application for all members of group chat, which could only be fixed by forcing the complete uninstall and reinstall. The bug was discovered by Check Point in August 2019 and reported to WhatsApp. It was fixed in version 2.19.246 onwards.
- In April 2020, the NSO Group held its governmental clients accountable for the allegation of human rights abuses by WhatsApp. In its revelation via documents received from the court, the group claimed that the lawsuit brought against the company by WhatsApp threatened to infringe on its clients' "national security and foreign policy concerns". However, according to research by Citizen Lab, the company did not reveal the end users' names, including Saudi Arabia, Bahrain, Kazakhstan, Morocco, Mexico and the United Arab Emirates.
- On December 16, 2020, a claim that WhatsApp gave Google access to private messages was included in the anti-trust case against the latter. However, as the complaint is heavily redacted due to being an ongoing case, it doesn't disclose whether this alleges tampering with the app's end-to-end encryption or simply Google accessing user backups.
- On November 29, 2021, an FBI document was uncovered by Rolling Stone, revealing that WhatsApp responds to warrants and subpoenas from law enforcement within minutes, providing user metadata to the authorities. The metadata includes the user's contact information and address book.
- In January 2022, an unsealed surveillance application revealed that WhatsApp started tracking seven users from China and Macau in November 2021, based on a request from DEA investigators. The app collected data on whom the users contacted and how often, as well as when and how they used the app. This is reportedly not a singular occurrence, as federal agencies can use the Electronic Communications Privacy Act to covertly track users without submitting any probable cause or linking a user's number to their identity.
- At the beginning of 2022, it was revealed that San Diego-based startup Boldend had developed tools to hack WhatsApp's encryption, gaining access to user data since its inception in 2017. The vulnerability was reportedly patched in January 2021. Boldend is financed, in part, by Peter Thiel, a notable investor in Facebook.
- In January 2022, an investigation by The Wire found that BJP, an Indian political party, allegedly used an app called Tek Fog which was capable of hacking inactive WhatsApp accounts en masse to mass message their contacts with propaganda. According to the Wire, a whistleblower with app access was able to hack a test WhatsApp account controlled by reporters "within minutes."
References

